Tech: Togo activist targeted by Indian-made spyware linked to cyber-mercenaries
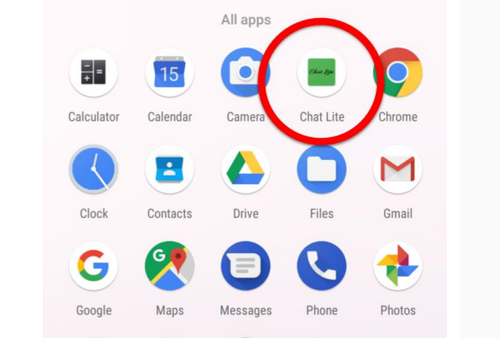
The spyware Android application masqueraded as a chat application named ChatLite © Amnesty
New investigation links Donot Team attacks and Innefu Labs, a cybersecurity company based in India
First time Donot Team linked to cyberattacks on activists outside South Asia
Spyware-loaded emails and fake Android applications could access device’s camera and microphone, steal photos and read WhatsApp messages
‘The surveillance industry is out of control with companies and cyber-mercenaries alike operating entirely in the shadows’ - Danna Ingleton
Activists in Togo risk being targeted by shadowy cyber-mercenaries who use covert digital attacks to steal victims’ private information to sell to private clients, a new Amnesty International investigation has revealed.
In a new 42-page report - Hackers for hire in West Africa: Activist in Togo attacked with Indian-made spyware - released today (7 Oct), Amnesty reveals how fake Android applications and spyware-loaded emails tied to the notorious Donot Team hacker group were used to target a prominent Togolese human rights defender to put them under unlawful surveillance.
The discovery is the first time Donot Team spyware has been found in attacks outside of South Asia. The investigation also discovered links between the spyware and infrastructure used in these attacks, and Innefu Labs, a cybersecurity company based in India.
The activist who was targeted, who wishes to remain anonymous, is a prominent voice for human rights in the country. Their devices were targeted between December 2019 and January last year, during a tense political period ahead of the 2020 Togolese presidential election.
Danna Ingleton, Deputy Director of Amnesty Tech, said:
“Across the world, cyber-mercenaries are unscrupulously cashing in on the unlawful surveillance of human rights defenders.
“Anyone can be a target - attackers living thousands of miles away can hack your phone or computer, watch where you go and who you talk to, and sell your private information to repressive governments and criminals.
“The surveillance industry is out of control with companies and cyber-mercenaries alike operating entirely in the shadows.
“Surveillance companies must stop putting profit over people and ensure repressive regimes are not using their technology to put a stranglehold on civil society.”
Persistent and malicious attacks
In this case, persistent attacks over WhatsApp and email attempted to trick the victim into installing a malicious application that masqueraded as a secure chat application. The application was in fact a piece of Android spyware designed to extract sensitive and personal information stored on the activist’s phone.
The spyware would have enabled attackers to access the camera and microphone, collect photos and files stored on the device, and even read encrypted WhatsApp messages as they were being sent and received. The covert nature of such attacks makes it extremely difficult for activists to detect whether their devices have been compromised.
The Togo-based human rights defender told Amnesty:
“Having realised that this was an attempt at digital espionage, I felt in danger. I can't believe that my work could be so disturbing to some people that they would try to spy on me. I am not the only one working for human rights in Togo. Why me?”
Amnesty’s investigation uncovered a trail of technical evidence left by the attackers which identified links between the attack infrastructure and Indian-based Innefu Labs. The company advertises digital security, data analytics and predictive policing services to law enforcement and armed forces, and claims to work with the Indian government.
Innefu Labs does not have a human rights policy and does not appear to carry out human rights due diligence - despite the enormous risks their products pose to society.
Amnesty has observed additional evidence of Donot Team attacks against organisations and individuals across South Asia, mostly concentrated in the north of India, Pakistan and Kashmir.
A shrinking space for human rights
The space for human rights work in Togo has rapidly shrunk in recent years. In 2019 the government introduced laws curtailing the rights to freedom of expression and peaceful assembly. There were also cases of human rights violations committed by the authorities, particularly against pro-democracy activists.
Several religious and opposition political figures in Togo have also reportedly been targeted with digital surveillance tools. Last August, The Guardian and Citizen Lab revealed that two Catholic clergy members - Bishop Benoît Alowonou and Father Pierre Chanel Affognon - recently revealed that hundreds of Togolese phone numbers were listed as potential targets of NSO Group’s Pegasus spyware. Those on the list included independent journalists and members of political opposition groups.
The threat of targeted surveillance, whether real or not, can inflict a huge psychological toll on activists and can have a devastating effect on their human rights work. Little is known about the “Wild West” cyber surveillance industry, despite Amnesty and other civil society’s repeated requests for more transparency. Even less is known about the flourishing hacker-for-hire industry.
As a result of its investigation, Amnesty is now calling on:
- Innefu Labs to publish in full the findings of an external audit it commissioned into links between its spyware tools and infrastructure used in the attack against the Togo activist. The company must also implement a human rights policy.
- The Indian government to investigate cyberattacks linked to Innefu Labs and take urgent action to ensure India-based surveillance companies are not involved in the targeting of activists - which is illegal under international human rights law.
- The Togolese government to ensure that everyone, including activists, is protected from human rights abuses, and to investigate and provide redress for any harm caused by cyberattacks carried out by private sector entities.
Response from Innefu Labs
In a written response to Amnesty, Innefu Labs denied “the existence of any link whatsoever between Innefu Labs and the spyware tools associated with the ‘Donot Team’” and the attack against the human rights activist in Togo. Innefu Labs also stated that they are not aware of any use of their IP address for the alleged activities.
There is no evidence to suggest Innefu Labs had a direct involvement or knowledge of the targeting of the human rights defender in Togo using the Donot Team spyware tools. The activity linked to the Donot Team may involve multiple distinct actors or organisations with access to the same custom spyware toolset and shared infrastructure.
Article details